Dark web monitoring solutions have become essential for organizations that want to stay ahead of cyber risks instead of reacting after damage is done. As cybercriminals increasingly trade stolen data, credentials, and sensitive information on hidden networks, the need for continuous visibility has never been greater.
Dark web monitoring solutions help organizations detect these threats early and reduce exposure before attackers can exploit them.
From leaked passwords to corporate data breaches, the dark web continues to serve as a hidden marketplace for illegal activity.
This is where dark web monitoring solutions play a critical role in modern cybersecurity strategies, offering real-time intelligence and early warning signals.
Why Dark Web Monitoring Solutions Matter Today
The digital ecosystem has expanded rapidly and so have attack surfaces. Businesses now operate across cloud platforms, mobile apps, APIs, and remote systems. In this environment, dark web monitoring solutions act as an early detection layer that scans underground sources where compromised data often appears first.
These solutions help security teams identify:
- Leaked credentials from data breaches
- Stolen customer or employee information
- Discussions among threat actors planning attacks
- Exposed corporate data being sold or shared
By identifying these risks early, dark web monitoring solutions reduce the time between breach and response, which is critical for minimizing damage.
How Dark Web Monitoring Solutions Work
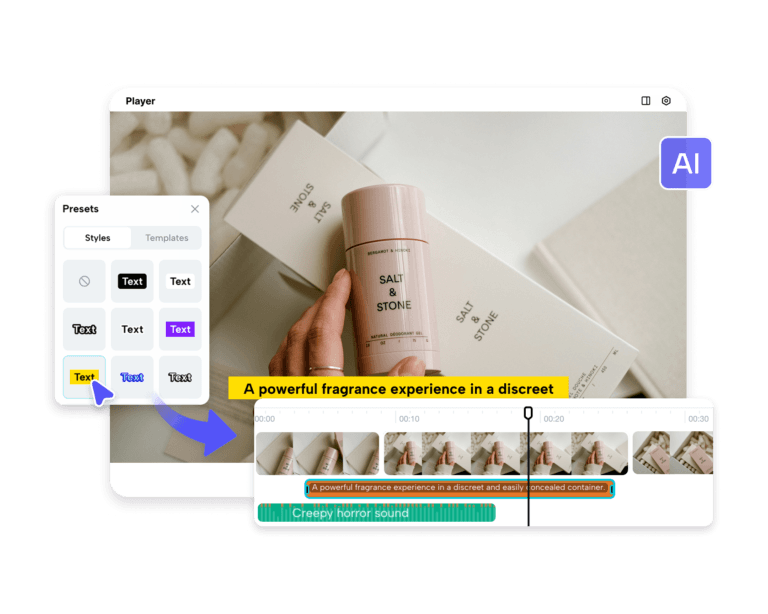
Modern dark web monitoring solutions operate by continuously scanning hidden areas of the internet, including TOR networks, I2P, ZeroNet, encrypted forums, and paste sites. These environments are often used by cybercriminals to exchange or sell stolen data.
Advanced systems combine machine learning, natural language processing, and human analyst review to convert raw data into actionable intelligence. This is what makes dark web monitoring solutions more effective than traditional security tools that only focus on internal networks.
The result is timely alerts that allow organizations to respond before exposed data turns into a full-scale breach.
Integration with Threat Intelligence Platforms
A strong cybersecurity strategy often combines dark web monitoring solutions with broader threat intelligence platforms. While dark web monitoring focuses on hidden and underground sources, threat intelligence platforms provide a wider view of global cyber threats, including malware campaigns, phishing infrastructure, and attacker tactics.
When used together, dark web monitoring solutions and threat intelligence solutions create a layered defense approach. This helps security teams connect external threats with internal vulnerabilities, improving overall decision-making and incident response.
Expanding Security with Attack Surface Protection Solutions
One of the biggest challenges in cybersecurity today is visibility. Organizations often struggle to track all digital assets exposed online. This is where attack surface protection solutions become important.
These solutions help identify and monitor all internet-facing assets such as domains, cloud services, APIs, and email servers. When combined with dark web monitoring solutions, they provide a complete picture of both exposed infrastructure and compromised data circulating on the dark web.
Together, attack surface protection solutions and dark web monitoring ensure organizations can detect both vulnerabilities and active exploitation attempts.
Strengthening Brand Security with Brand Protection Monitoring
Reputation is a critical business asset, and cybercriminals often exploit it through impersonation, fake domains, and phishing campaigns. Brand protection monitoring helps organizations track misuse of their brand identity across digital platforms, including dark web channels.
When integrated with dark web monitoring solutions, brand protection monitoring helps identify:
- Fake login pages targeting customers
- Stolen branding used in scam campaigns
- Data leaks affecting brand reputation
This combined visibility ensures that organizations can respond quickly to both technical and reputational threats.
The Role of Attack Surface Management in Cyber Defense
As digital environments grow, organizations need continuous visibility across all assets. attack surface management solutions and attack surface monitoring platform capabilities help security teams discover, map, and monitor all external-facing systems.
These solutions work alongside dark web monitoring solutions to close the gap between exposed assets and compromised data. By identifying vulnerabilities across cloud environments, mobile applications, and public repositories, they help reduce the chances of exploitation.
With attack surface protection solutions and attack surface management services, organizations gain continuous insight into their digital footprint and can act before attackers find weaknesses.
From Detection to Actionable Intelligence
What makes modern dark web monitoring solutions valuable is not just detection, but transformation of data into actionable intelligence. Security teams are often overwhelmed with raw threat data, but advanced systems prioritize and contextualize risks.
By combining automation with expert analysis, dark web monitoring solutions deliver alerts that are relevant, timely, and actionable. This enables faster incident response and stronger security outcomes.
Organizations that rely on dark web monitoring solutions are better positioned to prevent credential misuse, data breaches, and targeted attacks.
Building a Proactive Security Posture
Cybersecurity is no longer about reacting after an incident. It is about anticipating threats before they escalate. dark web monitoring solutions help organizations shift from reactive defense to proactive risk management.
When integrated with threat intelligence platforms, attack surface protection solutions, and brand protection monitoring, they create a unified security framework that improves visibility and response speed.
This layered approach ensures that organizations can detect risks early, understand attacker behavior, and reduce overall exposure.
Conclusion
As cyber threats continue to evolve, dark web monitoring solutions have become a core component of modern digital defense strategies. They provide early visibility into stolen data, attacker activity, and emerging risks across hidden online environments.
Cyble’s approach to dark web monitoring combines machine learning, NLP, and expert analysis to deliver real-time intelligence across TOR, I2P, ZeroNet, and other underground sources.
Alongside its attack surface and threat intelligence capabilities, it helps organizations strengthen visibility and respond to risks more effectively, without relying on fragmented tools or delayed detection.